Prevalence of Well Known Peers in the Internet of Things
Published 2014-07-04 originally at SAIFE's Blog as The Secure Internet of Things, Part 1: Prevalence of Well-Known Peers in the Internet of Things and cross-posted here.
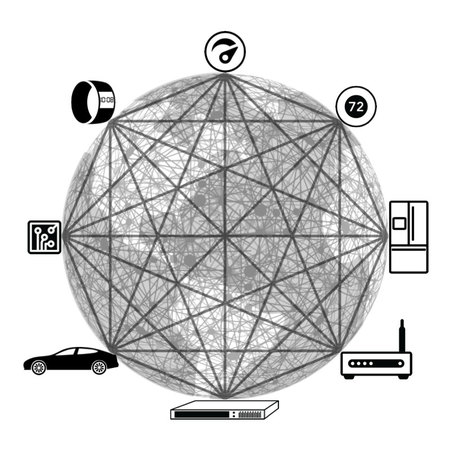
The Internet of Things is imagined to be a interconnection of sensors and physical devices of all kinds into the world’s information systems: a collection of machine-to-machine communication devices used to gather and distribute information about the world, contrasted with the human-machine interactions making up the bulk of today’s Internet. The machine-to-machine model places new restrictions on the common practices for security, as the standard practice of user authentication becomes troublesome without the regular involvement of a user.
There are an increasing number of people aiming to secure the Internet of Things before the industry gets too far along, lest we repeat the past. Cisco considers security for the IoT to be sufficiently problematic that they are conducting a Security Grand Challenge for the community to try and identify a path forward.
(My company, SAIFE Inc has submitted our re-imagined Public Key Infrastructure to the Security Grand Challenge.)
Authentication is the key
In the machine-to-machine model, the clearest security need is for authentication, yet much of the conversation is revolving around encryption - confidentiality. Confidentiality is interesting right now, given the state-actor wiretapping revelations in the last year, but confidentiality isn't the greatest need for my customer's humidity sensors.
When I work through the conceptual model of a connected warehouse, or the oil derrick of tomorrow, the questions that seem most pressing to me are:
- Whose sensor is this?
- Was the sensor legitimately built and purchased?
- Where should the sensor be allowed to transmit data?
- When should I stop trusting the sensor?
These are all more questions of authentication than encryption.
I believe that the most important piece to securing the Internet of Things is to fit one of our proven Public Authentication models to the micro-controllers that make up the most interesting Things.
Well Known Peers
Clemens Vasters at Microsoft wrote a post describing his need for the concept of well-known peers to solve transport security without the burden of a PKI. Particularly he:
want[s] to pair a device with a gateway, meaning that the peers are known a priori
For his machine-to-machine needs, the transmission paths, and thus the points of authentication, are dramatically more limited than those of a human on the Internet. These machines only need communicate with well-known peers, meaning a finite and rarely-changing set of other machines.
The idea of having a security solution where the parameters needed for communication are available to machines before they exchange data - where all peers that communicate are "well known" to each other - is the basis of the technology I've designed called SAIFE (pronounced "safe").
I will be writing on more topics related to the concept of simplifying Public Authentication.
Topics in the Series
- Prevalence of Well Known Peers in the Internet of Things
- Different PAN Parts: Auth-Only, Confidential and No Consequence
- Service Assisted Communication and Simplifying a PKI
- Service Assisted Communication’s Applicability to 6LoWPAN
- How Oracles Trivialize PKI Revocations, And Why That's Great
- Certificate-Based Routing In The Fog